
The corporate world is in a full-throttle sprint to integrate artificial intelligence, a race where the promise of unprecedented productivity is so dazzling that the caution signs marking significant security risks are being largely ignored. This high-stakes gamble, driven from the boardroom down,

The once-comfortable buffer that separated the discovery of a software flaw from its weaponization by cybercriminals has all but vanished, creating an unforgiving new reality where a disclosed vulnerability can become a global threat almost overnight. This dramatic acceleration in the cyberattack

The proliferation of small, low-altitude unmanned aerial systems has created a complex security challenge, demanding solutions that can reliably distinguish between genuine threats and benign activity in increasingly crowded skies. As drones become more accessible and capable, the potential for

The long-speculated shift from artisanal cyberattacks to industrialized, state-backed offensive operations is no longer a theoretical threat but a documented reality, fundamentally altering the calculus of global security. The rise of automated cyberattack systems represents a significant
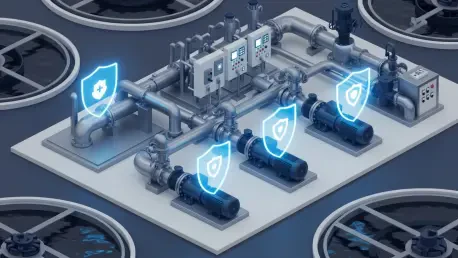
The silent hum of a water treatment facility's control room belies a vulnerability of national significance, where a few lines of malicious code could potentially shut off clean drinking water for millions of Americans. This stark scenario is no longer a work of fiction but a driving force behind a

Crafting a national cybersecurity framework that empowers federal agencies with vital threat intelligence without stifling the very businesses that form the backbone of the economy is one of the most complex challenges of modern governance. The U.S. Cybersecurity and Infrastructure Security Agency