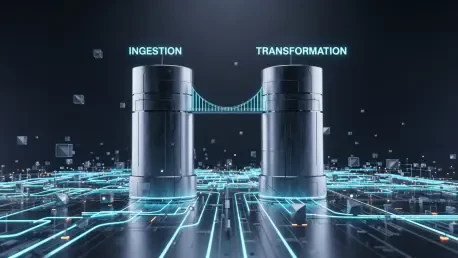
When the raw ingestion power of a leading data mover collides with the semantic precision of a transformation leader, the result is more than just a corporate marriage; it is a foundational shift in how enterprises architect their intelligence. The merger of Fivetran and dbt Labs represents a
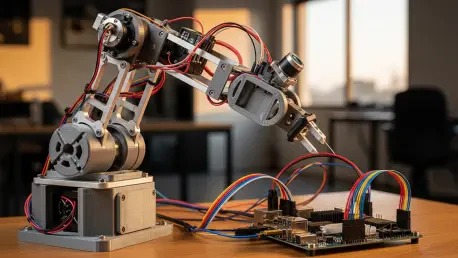
The massive concrete walls of industrial research facilities no longer hold a monopoly on the creation of sophisticated autonomous systems as the democratization of hardware continues to accelerate at an unprecedented pace. This fundamental shift mirrors the personal computer revolution that

The digital landscape in California is currently grappling with a legislative paradox that seeks to protect minors while potentially compromising the privacy of every adult user on the internet. Assembly Bill 1856 has emerged as a high-stakes follow-up to previous digital safety mandates,

Modern enterprises are currently navigating a landscape where the sheer volume of fragmented data prevents artificial intelligence from reaching its true operational potential. As of 2026, the primary challenge is no longer the collection of data but rather the efficient orchestration of it across

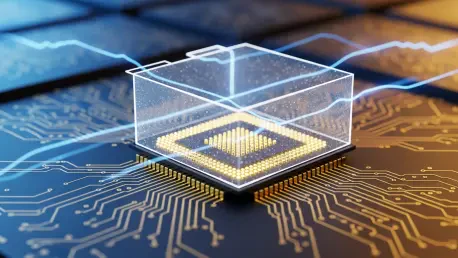
Modern enterprise data strategies require architectural resilience that legacy database systems simply cannot provide without introducing prohibitive complexity or massive overhead. This reality has driven the evolution of EDB Postgres Distributed (PGD), which serves as the mission-critical
The rapid proliferation of autonomous agentic systems has introduced a layer of complexity that traditional cybersecurity protocols struggle to address in a world where software acts with increasing independence. As these AI agents transition from simple chatbots to sophisticated entities capable
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45