With years of experience hardening some of the world’s most complex digital infrastructures, our expert today understands the exhaustion of managing fragmented security stacks. They have seen firsthand how the shift toward unified cloud operations isn’t just a technical upgrade but a fundamental change in how organizations defend their data. Today, we explore how centralizing disparate security signals—from endpoint identity to multi-cloud workloads—creates a more resilient posture and empowers teams to move at the speed of the cloud.
This conversation delves into the evolution of centralized security platforms, focusing on the transition from siloed monitoring to a unified operations layer. We examine the operational efficiencies of integrated third-party tools, the challenges of normalizing data across multi-cloud environments, and the strategic importance of external scanning in mitigating modern cyber threats.
Consolidating threat detection, vulnerability scanning, and sensitive data discovery into one interface changes how teams handle security signals. What impact does this unification have on incident response times, and what specific metrics should leadership track to measure the effectiveness of a centralized operations layer?
When you stop forcing analysts to pivot between GuardDuty for threats and Macie for data risks, you immediately eliminate the “swivel-chair” fatigue that slows down critical response. By bringing these signals into a single experience, teams spend significantly less time translating different formats and more time actually neutralizing threats in near real-time. I recommend that leadership track the “Mean Time to Act” rather than just the time to detect, as the automated analysis now does the heavy lifting of correlation for them. You should also watch the “Noise-to-Signal” ratio; a centralized layer is effective only if it reduces the thousands of raw findings into a manageable set of prioritized insights.
Utilizing a single bill and pay-as-you-go model for partner solutions like endpoint and identity security significantly streamlines procurement. What practical steps are involved in integrating these third-party tools into a unified architecture, and how do you prevent information overload when merging multiple vendor signals?
Integrating third-party tools like CrowdStrike, Okta, or Zscaler starts with utilizing the new Extended plan, which allows these partners to feed directly into the central security foundation. Organizations can select from 14 curated partner solutions at launch, including names like Splunk and Cyera, and deploy them without the friction of long-term contracts. To prevent information overload, you must leverage the unified operations layer’s ability to continuously analyze these disparate signals into a single view of risk. It is about shifting from a “collection” mindset to a “curation” mindset where the platform automatically surfaces only the most critical vulnerabilities and misconfigurations.
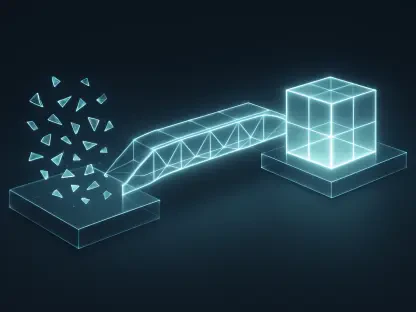
Maintaining a consistent security posture across multi-cloud environments requires a common data layer for disparate workloads. What are the biggest hurdles when normalizing security findings from different cloud providers, and how does real-time risk prioritization help teams focus on internet-facing exposures?
The most painful hurdle is the “language barrier” between different cloud providers, where a misconfiguration in one environment looks completely different in another. A common data layer solves this by acting as a universal translator, unifying security signals regardless of where the workload actually runs. Real-time risk prioritization then takes this normalized data and highlights the most dangerous paths, specifically those that lead to internet-facing exposures. This gives a security lead the peace of mind that their team isn’t chasing low-level internal alerts while a public-facing container remains unpatched and vulnerable.
Security scanning now encompasses virtual machines, containers, and serverless functions within a single view. How does this full-stack visibility influence the way developers and security teams collaborate, and what role does automated analysis play in managing the scale of these modern cloud resources?
Full-stack visibility ends the “blame game” between developers and security because everyone is looking at the same source of truth provided by expanded Amazon Inspector capabilities. When a container image or a serverless function shows a vulnerability, the automated analysis provides the context needed for a developer to fix it immediately without a long back-and-forth. This automation is the only way to keep up with the scale of modern cloud environments, where resources are spun up and down in seconds. It allows the security team to act as an enabler rather than a gatekeeper, providing consistent posture management across the entire application lifecycle.
External network scanning provides context about internet-facing exposure for resources not currently running in a primary cloud environment. How should organizations incorporate this external data into their existing vulnerability management lifecycle, and what are the trade-offs of relying on automated posture checks?
Organizations should treat external network scanning as an “outside-in” reality check that enriches the “inside-out” data they get from traditional agents. By incorporating this context, you can identify shadow IT or forgotten resources that aren’t yet under your primary management but still pose a massive risk to your multi-cloud estate. The main trade-off of relying on automated posture checks is the potential for a false sense of security if the rules aren’t updated to match your specific business logic. However, the benefit of continuous, automated scanning far outweighs this, as it catches the common misconfigurations that lead to the majority of data breaches today.
What is your forecast for multi-cloud security operations?
My forecast is that we are moving toward a “frictionless defense” model where the boundaries between different cloud providers become invisible to the security operator. In the coming months, as more multi-cloud capabilities are released, we will see a shift where security teams no longer manage tools, but instead manage global policies that follow the data everywhere it travels. We will see a massive reduction in the complexity of procurement and deployment, as the “seller of record” model becomes the standard for how enterprises build their security stacks. Ultimately, the future of security operations lies in this unified experience—one bill, one data layer, and one prioritized view of risk that covers the entire digital footprint.