

In a digital landscape where ownership of assets can often feel abstract and dependent on third-party platforms, the cryptocurrency sector continues to challenge the status quo by championing individual sovereignty. As reports of security breaches and frozen funds on centralized exchanges become

The automated systems now embedded in corporate life are no longer just efficient assistants for scheduling meetings and summarizing notes; they have quietly become powerful arbiters of personal identity. Across enterprises, AI is making assumptions about users based on signals like names, voices,

The promise of artificial intelligence has long been anchored in its conversational abilities, but a new wave of sophisticated digital agents is now decisively shifting the focus from simply talking to actively doing. This review explores Alibaba's new Qwen3.5 model, its key features, performance

The era of typing precise keywords into a search bar is rapidly drawing to a close, giving way to a more intuitive and conversational form of digital interaction that retailers are racing to accommodate. Salesforce has made a definitive move in this new landscape with its planned acquisition of

A leading figure from the decentralized, community-driven world of open-source artificial intelligence has made a pivotal move into the heart of the corporate AI establishment, signaling a major consolidation of talent in the race to develop autonomous agents. The recent announcement that Peter
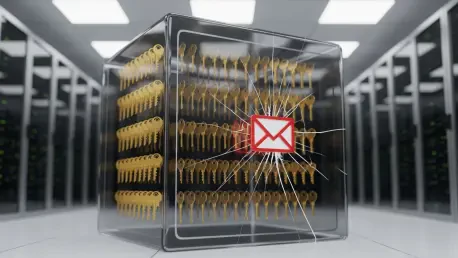
The very tools designed to be the ultimate guardians of our digital identities are now under intense scrutiny following a landmark academic study that exposed fundamental weaknesses in their core security architecture. A comprehensive investigation from ETH Zurich has revealed that the account

The nation's primary cyber defense agency is undertaking a profound and painful reorganization, signaling that the threat of a catastrophic digital attack on critical infrastructure is no longer a distant possibility but an imminent danger. Faced with a depleted workforce and dwindling resources,

Passionate about creating compelling visual stories through the analysis of big data, Chloe Maraina is a Business Intelligence expert with an aptitude for data science and a vision for the future of data management. Today, she joins us to demystify the Model Context Protocol (MCP), often called the

The rapid acceleration of artificial intelligence has created a significant dilemma for modern enterprises, forcing them to weigh the innovative power of cloud-native AI services against the non-negotiable demands of data security, regulatory compliance, and cost predictability that often

The once-comfortable buffer that separated the discovery of a software flaw from its weaponization by cybercriminals has all but vanished, creating an unforgiving new reality where a disclosed vulnerability can become a global threat almost overnight. This dramatic acceleration in the cyberattack
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy