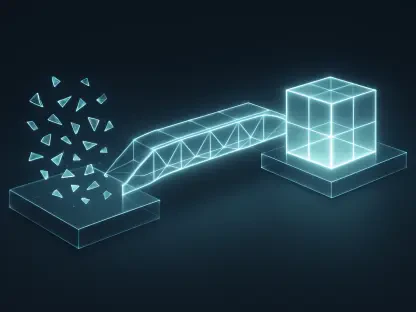
The traditional gap between identifying a critical security vulnerability and actually deploying a fix has long been the primary vector through which sophisticated threat actors compromise corporate networks. As organizations navigate the complexities of decentralized workforces and increasingly intricate digital infrastructures in 2026, the demand for a more agile response mechanism has never been more urgent. NinjaOne has addressed this challenge by launching a comprehensive vulnerability management solution that redefines the standard for IT operations by merging detection and remediation into a single, fluid process. Instead of relying on the disjointed hand-offs that typically occur between security analysts and IT administrators, this platform facilitates an immediate transition from discovery to resolution. By targeting the mean time to remediate as the primary metric of success, the system effectively closes the window of exposure that businesses previously accepted as an unavoidable risk.
Real-Time Visibility and the Elimination of Performance Bottlenecks
One of the most significant advancements within this framework is the utilization of AI-driven technology that continuously monitors for vulnerabilities using existing device telemetry. Unlike legacy systems that require heavy, agent-based scans which often result in CPU spikes and decreased employee productivity, this modern approach shifts the heavy lifting to the server side. This architectural choice ensures that identification processes occur silently in the background without impacting the end-user experience or the operational integrity of critical endpoints. By leveraging telemetry data that is already being collected for general management tasks, the platform identifies missing patches and configuration weaknesses in real time. This constant state of awareness allows IT departments to maintain a high level of security without the need for manual intervention or the scheduling of intrusive scan windows that frequently disrupt the standard business day.
Maintaining an accurate inventory of the security posture becomes particularly challenging when devices frequently disconnect from the corporate network or operate in disparate geographical locations. The integration of continuous monitoring ensures that even when an endpoint is offline, its last known state remains part of a centralized, up-to-date database that reflects potential risks. When the device eventually reconnects, the system immediately synchronizes and identifies any new vulnerabilities that may have emerged during its absence, ensuring no machine remains a blind spot for long. This level of visibility replaces the antiquated model of periodic, scheduled assessments which often left organizations unaware of critical flaws for weeks at a time. Consequently, IT professionals gain a reliable and comprehensive view of their entire environment, enabling them to address risks based on current data rather than outdated reports generated during the previous month’s audit cycle.
Orchestrating Collaborative Remediation through Autonomous Workflows
The synergy between IT and security departments is further solidified through the automation of patching workflows that span across both Windows and Linux environments. By linking vulnerability detection directly to remediation actions, the software removes the friction typically associated with exporting data from one tool and importing it into another. This automation allows for the prioritization of fixes based on the severity of the threat and the critical nature of the affected asset, effectively streamlining the decision-making process for busy administrators. Autonomous patching ensures that high-risk vulnerabilities are addressed as soon as a viable fix is identified, significantly reducing the administrative burden of manual deployments. As a result, technical teams are able to reallocate their bandwidth toward high-severity investigations and strategic projects rather than spending hours on repetitive, manual updates that can be handled more efficiently by an intelligent system.
Beyond simple automation, the platform introduces sophisticated patch confidence scoring to help IT professionals make informed choices regarding the reliability of specific updates. This feature evaluates the success rates of patches across a broad ecosystem, providing a safety net that prevents the deployment of updates known to cause system instability or software conflicts. Furthermore, the solution serves as a centralized system of record that simplifies the arduous tasks of compliance and auditing for various regulatory frameworks. By consolidating native remediation data with information imported from third-party scanners, the system generates continuous, audit-ready evidence of an organization’s security efforts. This unified approach not only enhances the speed of remediation but also ensures that every action is documented and verifiable, providing a clear trail of accountability that is essential for modern governance and risk management strategies in a global market.
Strengthening Posture through Proactive Infrastructure Management
The implementation of a unified vulnerability management strategy proved to be a decisive factor in modernizing corporate defenses against evolving digital threats. Organizations that moved away from fragmented security tools found that a consolidated platform allowed for a more coherent response to emerging exploits. Moving forward, technical leaders should prioritize the integration of real-time monitoring with automated response capabilities to maintain a resilient infrastructure. This transition required a shift in mindset from reactive patching to a proactive stance where security is an inherent part of the IT operational lifecycle. By adopting these advanced systems, businesses established a framework that not only mitigated immediate risks but also built long-term operational efficiency. Leaders evaluated their current toolsets and sought solutions that eliminated data silos, ensuring that security and IT teams functioned as a single, cohesive unit capable of defending the enterprise with unprecedented speed.
Actionable progress was achieved by those who embraced automated remediation as a cornerstone of their digital hygiene rather than a secondary consideration. The successful reduction of exposure windows depended on the ability of systems to act autonomously while still providing human operators with granular control and visibility. Organizations were encouraged to conduct regular reviews of their automation rules to ensure they aligned with the most current threat intelligence and internal compliance requirements. Furthermore, the focus shifted toward comprehensive coverage, where no device was left unmonitored regardless of its location or operating system. These steps provided a blueprint for future-proofing IT environments against the inevitable discovery of new software flaws. By maintaining a centralized record of all remediation activities, companies not only improved their security posture but also streamlined the reporting processes necessary for maintaining trust with stakeholders and regulatory bodies in an increasingly scrutinized landscape.