Chloe Maraina is a powerhouse in the world of business intelligence and data science, possessing a unique talent for transforming raw data into compelling visual narratives. With a background that blends technical rigour with a visionary approach to data management, she has spent years helping organizations navigate the complexities of cloud integration. Her insights into how data flows across borders make her one of the foremost experts on the evolving landscape of digital sovereignty. In this conversation, we explore the strategic shift toward regional security architectures and how enterprises are reclaiming control over their digital infrastructure.
We will delve into the critical differences between traditional cloud security and localized sovereign solutions, the operational benefits of shifting from hardware to SaaS-delivered models, and the long-term impact of data residency on corporate strategy.
Traditional SASE implementations often route traffic through regional gateways or log metadata outside the local jurisdiction. How does separating the data, control, and management planes within a specific region eliminate these security gaps, and what technical challenges arise when ensuring traffic is never “hairpinned” across borders?
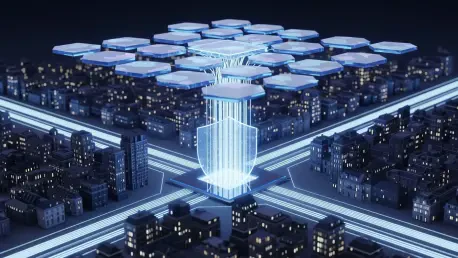
The beauty of a truly sovereign architecture is that it removes the invisible “detours” that data often takes in a traditional setup. In many legacy systems, you might have a local point of presence, but the actual decision-making—the control and management—is happening in a data center thousands of miles away. By anchoring the data, control, and management planes entirely within a region like the EU, we ensure that the inspection and logging stay local, which prevents the metadata from leaking into foreign jurisdictions. The technical hurdle is significant because you have to ensure the infrastructure is robust enough to handle full-stack processing without “hairpinning” traffic back to a central global hub for threat inspection. It requires a ground-up build that prioritizes local autonomy while maintaining the high-speed performance users expect from a global cloud leader.
Digital sovereignty has transitioned from a simple compliance checkbox to a strategic board-level priority. What specific risks do enterprises face when security gateways and operational controls reside outside their legal jurisdiction, and how do these risks impact long-term data residency strategies in regions like DACH?
When your operational controls reside outside your home jurisdiction, you are essentially operating under a different set of rules, which can lead to a “sovereignty gap” during legal disputes or regulatory shifts. For companies in the DACH region, this is a massive liability because their local laws regarding data protection are among the strictest in the world. If a security gateway is governed by an entity outside the EU, the enterprise risks having their data accessed or managed under foreign mandates that conflict with local requirements. This has forced boards to move beyond simple data storage and look at the entire lifecycle of data in motion, ensuring that legal entities like Versa Networks B.V. in the Netherlands provide a solid, EU-governed foundation. It’s a shift from a reactive compliance posture to a proactive defense of the company’s most valuable digital assets.
Many organizations attempt to achieve sovereignty by deploying appliances on-premises, yet true sovereignty requires clarity on where policy is enforced and who governs data in motion. How does a fully managed SaaS-style consumption model differ from these hardware-centric approaches in terms of operational complexity and staff requirements?
The old-school approach of stacking proprietary hardware in a local basement creates a mountain of operational complexity that most mid-sized firms simply can’t climb. You end up needing a specialized team of experts just to patch, update, and monitor those boxes, which distracts from the actual mission of the business. A fully managed SaaS-style model democratizes this technology, allowing companies to consume sovereign security with the same simplicity they expect from any other cloud service. It removes the need for building and staffing a private infrastructure, as the provider handles the heavy lifting of maintaining the sovereign boundary. This allows even smaller organizations to achieve a level of jurisdictional compliance that was previously the exclusive domain of global giants with massive resources.
Organizations often find that while their data is stored in sovereign clouds, the access points to that data remain governed by external entities. How should a company integrate sovereign SASE with their existing cloud initiatives to ensure Zero Trust policies are enforced entirely within sovereign boundaries?
It is a common frustration for IT leaders to realize their “sovereign” data is being accessed through a gateway that is anything but sovereign. To fix this, an enterprise must extend its sovereignty strategy beyond storage and into the very fabric of how users connect to applications. By integrating sovereign SASE, you ensure that every Zero Trust policy is enforced and every packet is inspected within the same legal boundaries where the data lives. This creates a cohesive “sovereign bubble” where the identity of the user and the integrity of the data are protected by the same regional laws. It effectively closes the back door that many cloud providers leave open when they route access through non-sovereign global infrastructure.
Establishing a sovereign infrastructure was previously limited to organizations with massive resources and specialized expertise. For a mid-sized enterprise, what is the step-by-step process for transitioning to a jurisdictionally compliant security stack, and what metrics should they use to measure the success of this migration?
The transition starts with a thorough audit to identify where traffic is currently being “hairpinned” or where management planes are operating across borders. Once those gaps are identified, the next step is to migrate to a cloud-delivered sovereign solution that offers full-stack architectural sovereignty, including logging and support within the region. Success isn’t just a “yes” on a compliance form; it should be measured by the reduction in latency caused by unnecessary traffic routing and the consolidation of legal contracts under a single regional entity. For a mid-sized firm, the ultimate metric is the ability to prove to auditors and customers that not a single bit of user metadata has left the sovereign jurisdiction. This level of transparency builds incredible trust and provides a competitive edge in markets where privacy is a top-tier demand.
What is your forecast for sovereign SASE?
I believe that within the next few years, sovereign SASE will transition from being a specialized requirement to the baseline standard for all global digital trade. We are moving away from a “one-size-fits-all” global internet toward a federated model where regional data fortresses protect local interests while still allowing for seamless global connectivity. As more governments assert authority over their digital borders, the demand for SaaS-delivered sovereign solutions will explode, making it impossible for vendors to compete unless they can prove their data, control, and management planes are legally anchored in the region they serve. It is an exciting time because we are finally building a digital world that respects the physical and legal boundaries of the people it serves.