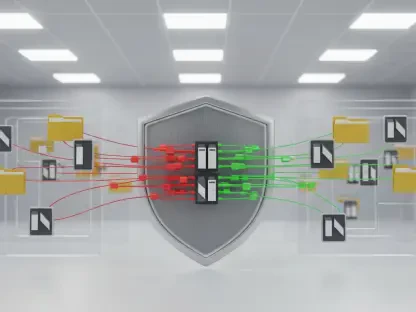
Modernenterprisesecurityteamsarecurrentlydrowninginarelentlessfloodoflow-fidelityalertsthatoftenobscuregenuinemaliciousactivitywithincomplexcloudenvironments. This persistent noise creates a dangerous environment where critical breaches can go undetected for weeks while analysts chase ghosts in the machine. In response to this systemic vulnerability, Tracebit has successfully secured $20 million in Series A funding, a round led by FirstMark Capital that arrives a mere eighteen months after their initial seed injection. The methodology involves the strategic placement of “canaries”—digital decoys such as fake credentials, shadow files, and simulated configurations—across a company’s cloud infrastructure. Unlike traditional monitoring tools that flag suspicious but potentially benign behavior, these assets have zero legitimate operational purpose. Consequently, any interaction with a canary serves as a definitive, high-confidence signal of unauthorized access. This shift from reactive monitoring to proactive deception represents a fundamental pivot in defensive strategy. By flooding the environment with deceptive markers, security leaders can effectively force attackers to succeed perfectly every time while the defenders only need them to make a single mistake. This investment reflects a growing confidence among major venture capital firms that automated deception is the most viable path to reclaiming the upper hand in cloud security operations.
Redefining Detection Precision Through Automated Integration
The traditional concept of “honeypots” has existed within the cybersecurity lexicon for several decades, yet the manual effort required to maintain such decoys often rendered them impractical for large-scale operations. Tracebit addresses this historical bottleneck by offering a turnkey, automated platform that integrates directly with existing security workflows and major cloud service providers. Instead of requiring a team of specialized engineers to craft individual traps, the system can deploy and manage millions of decoys across diverse environments with minimal oversight. Organizations like Riot Games, Docker, and Snyk have already integrated these capabilities to streamline their incident response protocols. This high-signal approach effectively eliminates “alert fatigue” because security operations centers can prioritize these notifications with absolute certainty. When a decoy credential is used or a hidden file is accessed, there is no ambiguity regarding the intent behind the action. Furthermore, this automation allows for the rapid rotation and updating of assets to match the evolving tactics of sophisticated threat actors. By making deception a fundamental layer of the infrastructure rather than a bolt-on addition, the platform ensures that the cost of an attack increases exponentially. This scalability is essential as businesses continue to expand their digital footprints across hybrid and multi-cloud architectures.
Implementing Proactive Defense: Strategic Steps for Security Resilience
The expansion of capital allowed Tracebit to refine its library of decoy assets and broaden its footprint across multiple cloud ecosystems, proving that simplicity often outperformed complexity in threat detection. Security leaders who successfully integrated these deceptive layers focused on three primary objectives to maximize their return on investment. First, they automated the deployment process to ensure that decoys remained synchronized with the constantly shifting landscape of ephemeral cloud resources. This eliminated the risk of stale or easily identifiable traps that savvy attackers might bypass. Second, they integrated the high-confidence signals directly into their existing orchestration and response tools, which enabled immediate, automated containment of compromised accounts the moment a canary was touched. Finally, the industry moved toward a philosophy of detecting the intruder rather than the exploit, which shifted the focus back toward basic attacker behavior rather than chasing every new vulnerability. These organizations discovered that by making their internal networks a minefield of deceptive data, they significantly reduced the dwell time of adversaries. This strategic pivot underscored a broader consensus that as infrastructure grew more intricate, the most effective defense relied on clear, undeniable signals of intent. Moving forward, the adoption of widespread deception became a standard prerequisite for any enterprise aiming to maintain a resilient and defensible cloud posture.