The integration of specialized repository management into broader deployment frameworks has historically been a fragmented endeavor that forced engineering teams to navigate between disconnected tools. The recent move by Harness to introduce its Artifact Registry into general availability signifies a transformative shift in how modern enterprises approach the preservation and distribution of their digital assets. By moving beyond the eighteen-month beta period, the platform now offers a cohesive environment where the storage of software components is no longer an isolated administrative task but an intrinsic part of the delivery lifecycle. This transition addresses a critical gap in the DevSecOps pipeline, where the lack of a centralized hub often led to security vulnerabilities and operational inefficiencies. As organizations grapple with the increasing complexity of software supply chains, the ability to govern every library and framework from a single interface provides a level of transparency that was previously unattainable for many large-scale engineering departments.
Bridging the Gap Between Development and Storage
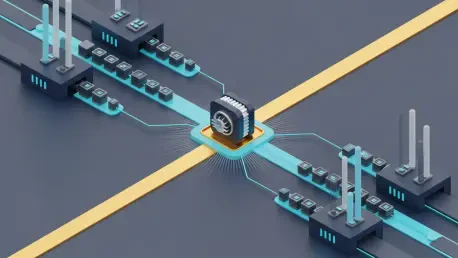
The fundamental architecture of the Harness Artifact Registry is built upon the principle that software artifacts should exist in a state of constant readiness rather than being relegated to passive storage silos. In the current landscape of 2026, developers frequently face friction when moving from the build phase to the distribution phase, often requiring manual hand-offs between disparate systems that do not share the same metadata or security context. Harness eliminates this barrier by providing deep, native integration that allows for the automatic ingestion of build outputs directly into a governed repository. This structural alignment ensures that third-party dependencies and internal libraries are managed under a unified set of protocols, which significantly reduces the time spent on troubleshooting environment-specific discrepancies. By supporting an extensive array of package ecosystems, the platform caters to the diverse needs of polyglot development teams who require a consistent experience regardless of the programming languages or frameworks they utilize.
Operational efficiency is further enhanced by the registry’s emphasis on reducing the cognitive load on individual contributors who previously had to maintain complex repository configurations across multiple environments. The inclusion of advanced features such as AI-driven automation and immutability settings ensures that the integrity of every component is preserved from the moment it is created until it reaches a production environment. This proactive stance on lifecycle management allows organizations to enforce retention policies and versioning standards without the need for constant manual intervention by DevOps engineers. As the platform continues to evolve through 2027 and 2028, the focus on providing a seamless user experience will likely become a primary differentiator for companies seeking to scale their software delivery capabilities without linear increases in headcount. The result is a more resilient development ecosystem where the focus remains on innovation rather than the maintenance of the underlying infrastructure that supports it.
Consolidation as a Strategic Market Advantage
The emergence of a native artifact management solution within the Harness ecosystem represents a significant strategic challenge to established industry leaders like JFrog and Sonatype. For nearly a decade, these specialized vendors have defined the repository market by offering deep, feature-rich tools that addressed the specific needs of package management in isolation. However, the current enterprise trend favors platform consolidation over the best-of-breed approach that previously dominated the tech stack. Modern IT leaders are increasingly prioritizing the reduction of tool sprawl to minimize the overhead associated with managing separate licenses, support contracts, and integration points. By embedding repository functionality directly into the CI/CD pipeline, Harness offers an alternative that makes the traditional multi-vendor setup seem unnecessarily complex. This shift is particularly appealing to organizations that have already standardized on the Harness platform for their deployment needs and are looking to extend that governance.
One of the most compelling arguments for this consolidated model is the inherent consistency it brings to identity and access management across the entire software development lifecycle. In a fragmented environment, security teams must synchronize permissions across various platforms, a process that is prone to human error and often results in overly permissive access rights. Harness addresses this by utilizing a single IAM framework that spans both the delivery pipelines and the artifact repositories, ensuring that a developer’s permissions remain consistent as they move from writing code to publishing packages. This architectural unity closes the security gaps that frequently emerge at the boundaries between different tools, providing a more robust defense against unauthorized access or accidental configuration errors. Furthermore, the ability to apply the same policy engine to both deployment workflows and stored assets allows for a level of governance that is difficult to achieve when working with standalone tools that require separate policy definitions.
Mitigating Risks Within the Modern Supply Chain
The practical necessity of a centralized and governed registry becomes evident when examining the risks associated with legacy software environments and fragmented internal processes. Many large enterprises still struggle with assets that are stored in unmanaged locations, such as insecure network file shares or temporary pipeline storage, which lack the audit trails required for modern compliance. These dark artifacts represent a significant blind spot in the corporate security posture, as they can be easily manipulated or replaced by malicious actors without detection. Harness mitigates these vulnerabilities by providing a highly visible, governed environment where every piece of code is tracked and verified. For companies dealing with rigorous regulatory requirements, the transition to a unified registry provides the necessary documentation to prove a consistent chain of custody for every software component. This transparency is essential for maintaining trust with customers and partners who demand higher levels of assurance regarding the software they consume.
Beyond the immediate security benefits, the consolidation of artifact management into a primary DevSecOps platform yields substantial operational improvements for engineering leadership. By streamlining the number of credentials and management interfaces that developers must interact with, organizations can significantly reduce the toil that often slows down the delivery process. This reduction in administrative friction allows teams to focus more on feature development and less on the plumbing of their CI/CD systems. In large-scale transformations, like those seen at renewable energy firms or financial institutions, the ability to manage complex software design through a single pane of glass is a major factor in improving overall agility. The transition to such a platform ensures that as the organization grows, its security and governance standards remain enforceable across all projects, preventing the emergence of silos that could lead to future technical debt or unmitigated risks in the production environment.
Proactive Defense: The Dependency Firewall
The introduction of the Dependency Firewall within the Harness Artifact Registry marks a critical evolution from reactive vulnerability scanning to proactive threat prevention. In an environment where open-source packages are frequently targeted by supply chain attackers, the ability to block non-compliant or malicious code before it enters the internal development ecosystem is a vital defense mechanism. This firewall operates by applying granular policies to incoming packages, evaluating them against security, licensing, and quality standards established by the organization. Unlike traditional methods that scan code after it has already been integrated into a project, this proactive approach ensures that developers are only working with vetted and approved components. This architectural decision fundamentally changes the relationship between security and development, turning a potential bottleneck into a native part of the ingestion process that does not impede the speed of the engineering teams.
The strategic advantage of this firewall is amplified by Harness’s role as the primary orchestrator of the delivery pipeline. While other repository vendors offer similar gatekeeping features, they often function as external hurdles that developers must navigate outside of their standard workflow. Because Harness owns the pipeline, it can embed these security controls directly into the delivery process, making governance a natural consequence of the build. This means that if a package is flagged as risky, the pipeline can be automatically halted or the package quarantined before it can cause any downstream damage. This level of control is essential for maintaining a secure software supply chain in 2026, as the volume of third-party dependencies continues to grow. By providing a mechanism to enforce security at the point of entry, Harness empowers organizations to take a more aggressive stance against emerging threats while maintaining the high velocity required by modern business demands.
High-Velocity Governance in the AI Era
As the industry moves deeper into 2026, the rapid adoption of artificial intelligence in software development has introduced a new dimension of risk that traditional governance models are ill-equipped to handle. AI agents are now capable of generating and committing code at speeds that far exceed human capacity, which places an immense strain on existing verification processes. The Harness Artifact Registry serves as the ultimate arbiter in this high-velocity environment, ensuring that even AI-generated components are subjected to the same rigorous standards as manually written code. Without a robust, automated registry to verify the integrity and origin of every asset, organizations risk being overwhelmed by a flood of unvetted code that could introduce significant vulnerabilities. The registry acts as a stabilizing force, providing the necessary checks and balances to ensure that rapid innovation does not lead to a compromise in operational security or architectural stability.
Maintaining a verifiable chain of custody has transitioned from a best practice to an absolute requirement for modern enterprise software delivery. Organizations must be able to trace every component back to its source and verify its integrity at every stage of the lifecycle. The Harness platform provides this level of traceability by centralizing the management of all assets and providing detailed logs of every interaction. This is particularly important when dealing with the opaque nature of some AI-generated code, where understanding the provenance of a specific library or function is critical for risk assessment. By governing the building blocks of development, Harness helps companies maintain a high level of confidence in their production environments. The result is a balanced approach where the benefits of AI-driven speed are realized without sacrificing the security and compliance standards that are vital for long-term organizational health and the protection of the digital supply chain.
Actionable Steps for DevSecOps Implementation
The successful launch of the Harness Artifact Registry demonstrated that the transition toward integrated platform governance was a necessary evolution for managing complex software delivery. Organizations that consolidated their toolchains into a single, unified environment significantly reduced their exposure to supply chain vulnerabilities while simultaneously improving developer productivity. The historical data from 2026 indicated that firms adopting proactive defense mechanisms, such as the Dependency Firewall, were far less likely to suffer from large-scale security breaches related to compromised third-party packages. Leaders in the engineering space moved away from the administrative burdens of multi-vendor setups, favoring instead the streamlined policy enforcement and identity management provided by all-in-one platforms. This shift allowed security teams to become enablers of innovation rather than barriers, as governance was built directly into the automated workflows that powered the business.
Future strategies for DevSecOps must prioritize the elimination of silos between storage and deployment to ensure that no software asset remains unmanaged or untracked. Stakeholders should evaluate their existing repository infrastructure for gaps in visibility and policy enforcement, particularly as AI-generated code becomes a larger portion of the total codebase. Implementing a centralized registry with native pipeline integration was the most effective way to establish a reliable chain of custody and maintain operational integrity. By focusing on proactive gatekeeping rather than reactive scanning, organizations successfully secured their supply chains against increasingly sophisticated threats. The move toward a more integrated approach provided the flexibility needed to adapt to changing market conditions while ensuring that security remained a core component of every build. Organizations that ignored these integration trends faced higher operational costs and increased risks, proving that the future of software delivery belonged to those who embraced unified orchestration.