The global digital landscape remains under constant siege as foreign intelligence services weaponize web infrastructure to launch destructive campaigns and manipulate public perception. This research evaluates the impact of recent federal court-ordered domain seizures on the operational agility of Iranian-backed actors, specifically those tied to the Ministry of Intelligence and Security (MOIS). By examining the intersection of international law and cyber warfare, the study seeks to determine if removing these digital outposts truly handicaps sophisticated state actors or merely forces a temporary relocation of their activities.
The challenge lies in the inherent flexibility of cloud-based infrastructure, where groups like “Handala” operate with significant technical backing. While these legal interventions serve as a visible pushback against foreign aggression, the effectiveness of such measures is often debated among national security experts. This analysis addresses whether the current strategy of infrastructure takedowns is an adequate defense for critical sectors or if the speed of digital reconstitution renders these legal victories largely symbolic.
Background: The Rise of Iranian Sabotage and Political Intimidation
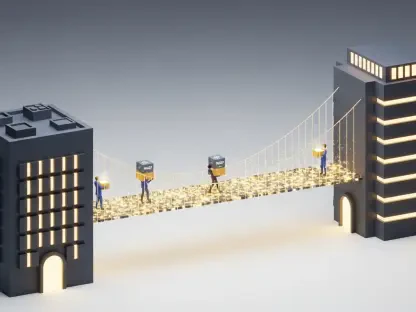
Recent operations by the Department of Justice and the FBI led to the seizure of four primary domains utilized by Iranian intelligence to facilitate high-stakes cyberattacks and influence operations. These sites were not merely informational; they acted as operational hubs for facilitating destructive breaches, including a massive compromise of Stryker, a major medical technology firm. The breach was particularly alarming because it showcased how digital sabotage can lead to real-world consequences, forcing several hospitals in Maryland to disconnect their networks to prevent widespread data loss.
Beyond industrial sabotage, the targeted infrastructure supported a broader campaign of political intimidation and harassment against dissidents and journalists. By using these platforms to leak stolen data and issue threats, the MOIS attempted to project power and silence opposition across international borders. Understanding the role of these domains is essential for identifying how foreign adversaries leverage the open nature of the internet to conduct both clandestine espionage and overt psychological warfare against democratic institutions and critical infrastructure.
Research Methodology, Findings, and Implications
Methodology
This study employed a comprehensive case-study framework, synthesizing federal court records, DOJ official statements, and technical incident reports linked to Handala’s recent activities. The investigation prioritized a forensic look at the Stryker breach, specifically focusing on how the attackers weaponized Microsoft Intune to gain administrative control over thousands of endpoint devices. To gauge the broader strategic impact, researchers integrated expert commentary from the Foundation for Defense of Democracies and former high-ranking FBI officials to analyze the logistical hurdles Iran faces when replacing seized digital assets.
Findings
The data revealed that while the seizure of these four domains successfully deactivated the immediate platforms used for publicizing the Stryker attack, the MOIS maintains a highly redundant infrastructure. The investigation showed that Handala and similar groups are capable of migrating their data and launching replacement domains in under twenty-four hours. Although the legal action disrupted the visibility of their influence campaigns for a brief window, it did not significantly deplete their technical resources or long-term capability to execute administrative-level wipes on target networks.
Implications
These findings suggest that domain seizures, while legally necessary to disrupt criminal activity within US jurisdiction, are insufficient as a primary defense against state-sponsored threats. For critical infrastructure providers, the evidence implies that internal network resilience and hardware-level security are more reliable than government-led infrastructure takedowns. The results also indicate that without deeper international cooperation to tighten domain registration requirements, state actors will continue to treat these legal disruptions as minor operational inconveniences rather than existential threats.
Reflection and Future Directions
Reflection
The research highlighted a persistent imbalance between the slow pace of legal proceedings and the rapid-fire nature of cyber warfare. A notable obstacle in the study was the difficulty of quantifying the psychological impact on the threat actors, as they remain insulated from American law enforcement within their own borders. While the study effectively mapped the transition toward using legitimate administrative tools for sabotage, it lacked access to the internal financial ledgers of the MOIS, which would have clarified the exact cost of replacing these seized assets.
Future Directions
Future inquiries should prioritize the development of “active defense” models that target the software supply chains and command-and-control protocols rather than just the public-facing domains. Investigating how automated registration systems can be hardened against known state-linked personas could offer a more permanent barrier to infrastructure regrowth. Additionally, there is a clear need for research into how private-sector collaboration with international registrars could be streamlined to mirror the speed of the adversaries they are attempting to block.
Conclusion: The Limits of Legal Intervention in a Borderless Workspace
The investigation into Iranian-linked domain seizures demonstrated that legal maneuvers provided a necessary but fleeting barrier to state-sponsored cybercrime. Federal authorities took decisive action to reclaim digital territory, yet the adaptability of groups like Handala showed that the battle for infrastructure is a continuous cycle of displacement. This effort proved that while the government can shutter specific portals of intimidation, the underlying technical expertise of the MOIS remained intact and ready to pivot toward new digital environments.
Moving forward, stakeholders should have focused on integrating automated threat detection with proactive legal frameworks to close the window of opportunity for threat actors. Strengthening the security of administrative tools like Microsoft Intune became a higher priority than simply chasing domains across various registrars. Ultimately, the path to true security required a shift from reactive litigation to a philosophy of systemic resilience, ensuring that the next wave of infrastructure-based attacks would find no purchase in a hardened and alert digital ecosystem.