

The transition from a hardware-centric identity to a software-defined intelligence platform marks a definitive turning point for a company that once defined the flash storage market. Pure Storage has officially embraced the name Everpure to reflect its evolution into a provider of automated, living

The rapid transition of digital information from a secondary operational asset to the literal pulse of the global enterprise has forced a massive reevaluation of how back-end systems function in the current market. As the competitive race for artificial intelligence dominance reaches a fever pitch,

The accelerated convergence of high-performance silicon and enterprise-grade open-source orchestration is no longer a technical luxury but a fundamental requirement for businesses attempting to transition from experimental algorithms to industrial-scale automation. As the global artificial
The global landscape of digital communication underwent a fundamental shift with the introduction of sophisticated linguistic frameworks that fundamentally altered how machines interpret human intent and structural nuance. When the OSCParaphraseSC 2021 framework emerged, it represented more than a

The traditional image of a software engineer meticulously hand-crafting every semicolon and bracket has been replaced by a professional who orchestrates a complex symphony of autonomous agents and generative models. This seismic shift marks a departure from low-level manual construction toward

Modern enterprises are discovering that the financial burden of moving data in real-time often outweighs the competitive advantages they hope to gain from their expensive artificial intelligence models. While the promise of instantaneous insight remains a powerful motivator, the reality of

Chloe Maraina is a specialist in transforming complex datasets into visual narratives, bringing a sharp eye for software supply chain security and the evolving risks of agentic AI. With her extensive background in business intelligence and data science, she bridges the gap between raw code
The rapid assimilation of machine learning into the bedrock of corporate strategy has fundamentally altered the way executives view the relationship between algorithmic output and operational risk. In the current landscape, the novelty of a generative response or a predictive score has been

In a landscape where supply chains are becoming increasingly fragmented and outsourced, the ability to translate raw data into actionable intelligence is what separates market leaders from those struggling with overhead. Chloe Maraina has spent her career at this intersection, utilizing her
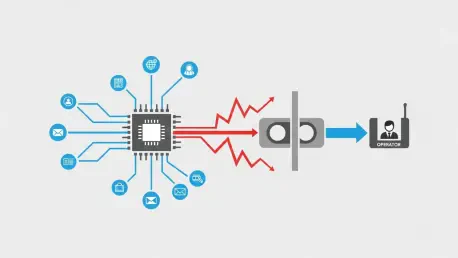
The initial demonstration of a fully autonomous AI agent can evoke a feeling of cold dread rather than pure excitement for those responsible for enterprise architecture. While these agents promise unprecedented levels of automation and efficiency, they simultaneously introduce a fundamental and
ITCurated uses cookies to personalize your experience on our website. By continuing to use this site, you agree to our Cookie Policy